SEC Obtains Default Judgment in Edgar Hacking Case
On July 29, 2021, the United States District Court for the District of New Jersey entered a default judgment against Oleksandr Ieremenko and Andrey Sarafanov, who were charged in connection with a scheme to trade on nonpublic earnings information hacked from the SEC’s EDGAR system.
The SEC’s complaint alleged that Ieremenko, a Ukrainian hacker, gained access to EDGAR in 2016 and extracted EDGAR filings containing nonpublic earnings results.
The information in the filings was allegedly passed to individuals, including Sarafanov, who used it to trade in the narrow window between when the files were extracted from SEC systems and when the companies released the information to the public.
In total, eight traders allegedly traded before at least 157 earnings releases from May to October 2016 and generated at least $4.1 million in illegal profits. According to the complaint, Sarafanov’s trading on hacked information resulted in profits of $1,094,435.
Ieremenko and Sarafanov did not answer or otherwise respond to the SEC’s complaint.
In its order entering a default judgment, the court permanently enjoined Ieremenko and Sarafanov from violating the antifraud provisions of Section 10(b) of the Securities Exchange Act of 1934 and Rule 10b-5 thereunder and Section 17(a) of the Securities Act of 1933. The court also ordered Ieremenko and Sarafanov to pay penalties of $12,405,045 and $3,283,305, respectively.
Ieremenko and Sarafino were also Indicted for the scheme.
This is the second Indictment for Ieremenko. He was previously charged by the Department of Justice in 2015 with securities fraud in connection with another hacking scheme.
According to that Indictment, from about February 2010 through 2015, Ieremenko and four other defendants engaged in an international computer hacking and fraudulent securities trading scheme whereby they: (a) hacked into the computer networks of Marketwired L.P., PR Newswire Association LLC, and Business Wire; (b) stole confidential press releases containing material nonpublic information from the Victim Newswires’ internal computer networks prior to their public release; and (c) traded ahead of the material nonpublic information contained in the stolen releases before its distribution to the investing public.
During the course of the scheme, the defendants accessed more than 150,000 stolen releases and executed profitable trades based on the material nonpublic information contained in the stolen releases. In total, the scheme generated more than $30 million in illicit trading profits.
That case is still open.
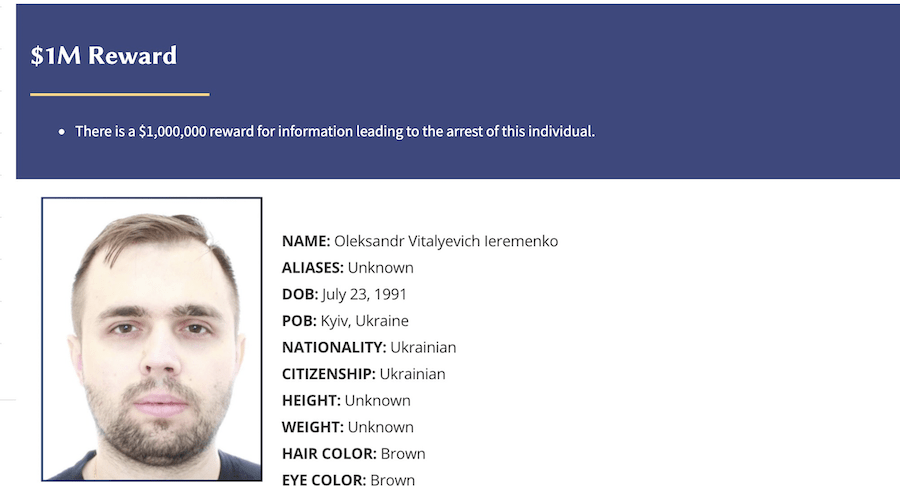
Ieremenko, who remains at large, is now listed as a “Most Wanted Fugitive” on the United States Secret Service website, with a $1,000,000 reward for information leading to his arrest.
For further information about this securities law blog post, please contact Brenda Hamilton, Securities Attorney at 101 Plaza Real S, Suite 202 N, Boca Raton, Florida, (561) 416-8956, by email [email protected] or visit www.securitieslawyer101.com. This securities law blog post is provided as a general informational service to clients and friends of Hamilton & Associates Law Group and should not be construed as and does not constitute legal advice on any specific matter, nor does this message create an attorney-client relationship. Please note that the prior results discussed herein do not guarantee similar outcomes.
Hamilton & Associates | Securities Lawyers
Brenda Hamilton, Securities Attorney
165 E, Palmetto Park, Second Floor
Boca Raton, Florida 33432
Telephone 561-416-8956